You don’t need to be a networking guru to have come across the term ping while working with computers, setting up networking devices such as wireless routers, dealing with online applications, or playing games online. If you’re wondering what ping means and what the ping command does, read on. In this guide, I’ll explain how ping works, what you can use it for, and what information you’ll get by running ping on a Windows computer. There’s some ground to cover, so, without further ado, let’s start:
What is ping?
Ping is a diagnostic tool that you can use to test if a host, such as a web server, a wireless router, or another computer can be reached. In simpler words, ping can tell you whether your computer can communicate with the host you specify.
What a ping command looks like
How does ping work?
Ping works on any Internet Protocol (IP) network, and it operates by sending Internet Control Message Protocol (ICMP) Echo Request messages. These messages are tiny packets of data sent from your computer by the ping command to a target host. In return, the host that receives them sends back responses called Echo Replies. When this whole process ends, ping measures the time it took for the message to go forth and back.
What is ping in networking tests and games?
The round-trip time is calculated in milliseconds (ms), and it tells you how fast the communication, or the network latency, if you prefer, is between the two hosts. If the response times are high or if ping tells you packets were lost, there’s a problem with the network connection. On the other hand, if the ping command shows that no packets were lost and the response times are low, the network connection is in good shape.
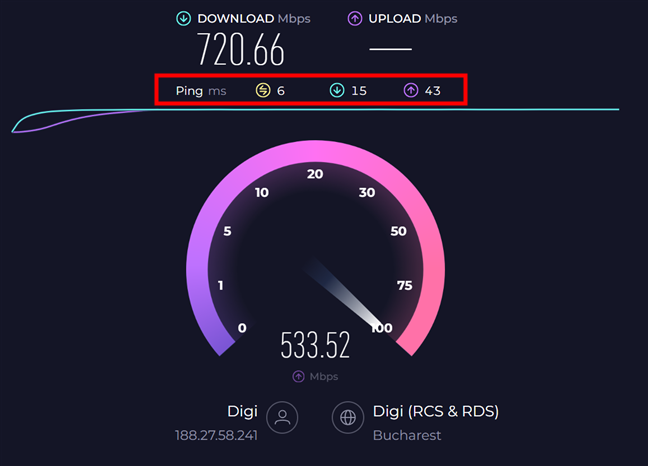
Ping results in SpeedTest
What you need to remember is that when you see ping values reported in apps, in networking tests like SpeedTest, or in online games, they refer to the time it takes for your PC to get a response to ping commands. This time is an indicator of the speed of the reaction time of your internet connection or your network connection. The lower the ping, the better the reaction time.
What operating systems and devices support the ping command?
You can use the ping command tool in Windows 10, Windows 11, Linux distributions, macOS, Unix, and FreeBSD, as well as in many other operating systems. It works on desktop computers, laptops, tablets, servers, etc. Even networking equipment like Wi-Fi routers implement ping for troubleshooting network problems.
Understanding the results of a ping command
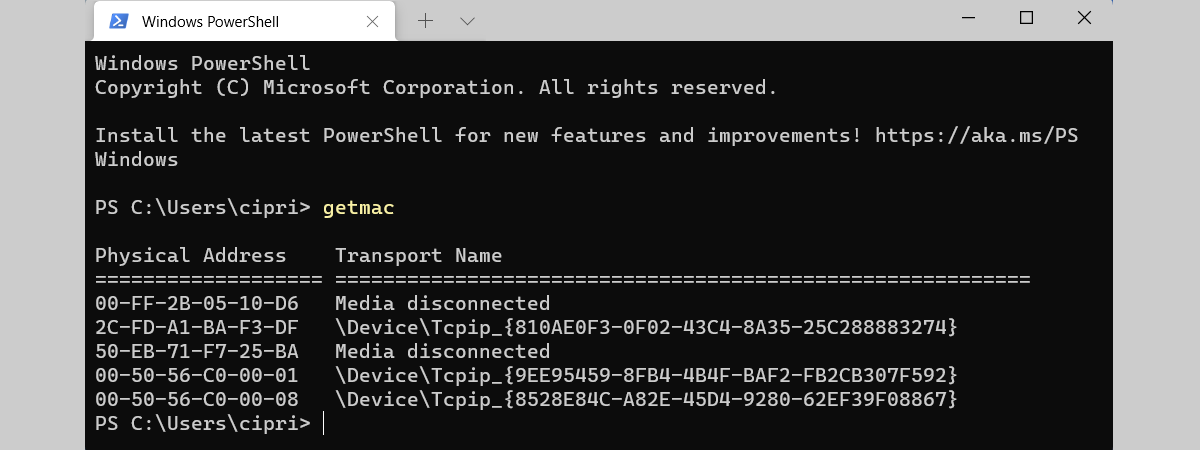
So, now we know that the ping command is useful mostly for troubleshooting the accessibility of devices on the network and the internet. But let’s break it down and see what it provides on a Windows computer. When running a ping command, you determine:
- Whether the target of the ping command is active or inactive.
- How much time it takes to communicate with the target device to send and receive an Echo request and a reply.
- How many packets are lost when communicating with the target device.
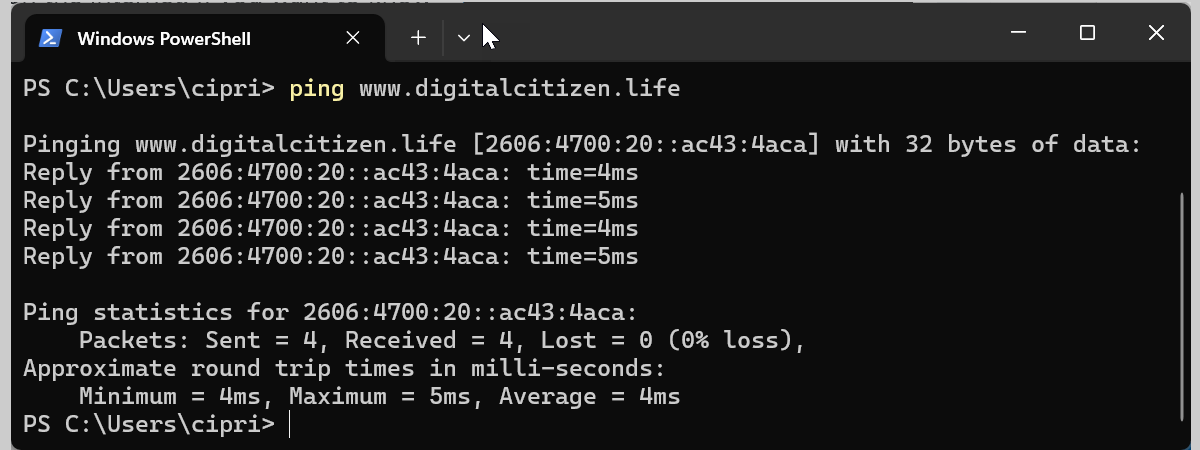
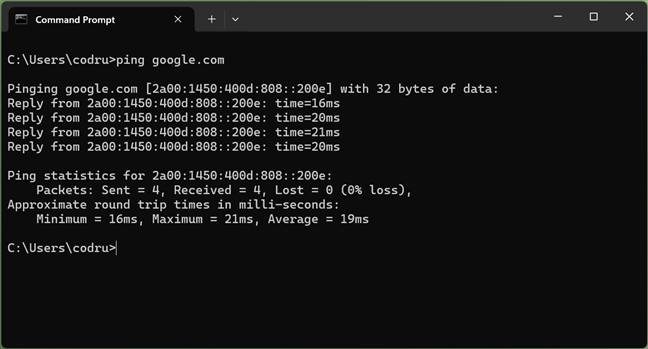
Take a look at the screenshot below, where I ran the command:
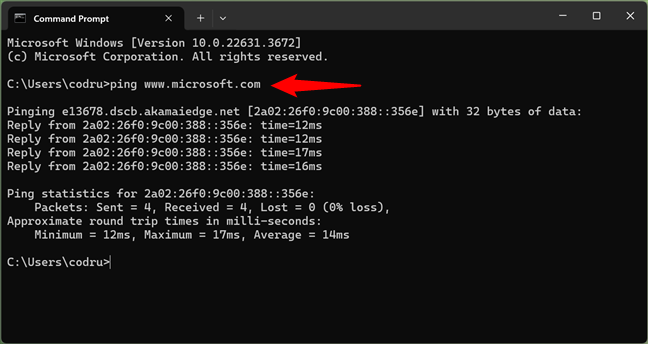
How to run and what you get from a ping command in Windows
From the output of this ping command, you learn:
- That the www.microsoft.com website is available and reachable from my Windows PC because I got a reply
- The IPv6 address of the microsoft.com website. It is the weird address displayed between square brackets on the first line of results and also on the line that starts with “Ping statistics for…”
- That there was no data loss in my connection to the microsoft.com website
- The time it took, in milliseconds, for microsoft.com to reply to the ping command: for each of the four Echo requests individually, the minimum, the maximum, and the average time it took to respond to the ping command
As you can see, ping sends four Echo requests by default, and it shares statistics and data based on the replies it gets from the target. Now let’s take a look at how to use ping commands on a Windows computer:
How to run ping commands in Windows
Before anything else, keep in mind that in Windows, you can execute ping commands from Command Prompt, PowerShell, or Terminal. Everything works the same regardless of which command-line environment you prefer, and it doesn’t matter whether you’re using Windows 10 or Windows 11.
To begin, open the Command Prompt or PowerShell. Then, enter ping followed by the IP address (or the hostname) of the target computer or device. For example, type something like
or
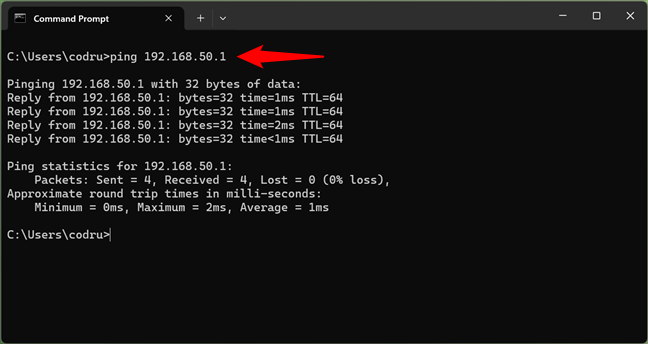
How to ping in CMD
As documented by Microsoft, the ping command in Windows can use lots of parameters. To see them for yourself, write
or
…and press Enter on your keyboard. Windows then lists all the parameters and switches you can use for the ping command.
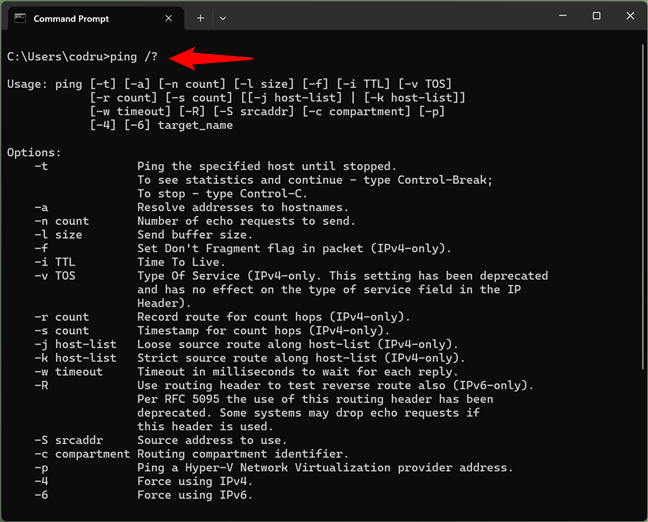
How to see the parameters of ping in CMD
NOTE: You can use / or - before any parameter of the ping command. They are interchangeable and lead to the same result.
Options for the ping command in Windows
Here is an explanation of all the switches for the ping command:
- /t - ping continues sending Echo request messages to the destination until interrupted manually. To interrupt and display statistics, press CTRL + Pause/Break. To interrupt and quit the ping, press CTRL + C.
- /a - the ping tries to resolve and show the hostname of an IP address that is entered as the target.
- /n count - use this to change the number of Echo request messages from 4 (the default) to something else. You can use any number from 1 to 4294967295.
- /l size - sets the size (in bytes) of the Echo request message that is sent to the target from 32 (the default) to something else. You can use any number from 1 to 65527.
- /f - use this to send Echo request messages with a “Do Not Fragment” flag turned on, to prevent the request from being fragmented by routers on the way to the destination. This option works for IPv4 addresses only, and it is useful for troubleshooting path Maximum Transmission Unit (PMTU) problems.
- /i TTL - sets the Time to Live (TTL) value for the Echo request, the maximum of which is 255. TTL limits the lifetime of the data being sent by the ping command. If the TTL value has elapsed and no reply was received, the data is discarded.
- /v TOS - sets the Type of Service (TOS) used for the Echo request. The default value is 0, and the maximum is 255. This option works only for IPv4 addresses.
- /r count - sets the number of hops between your PC and the target that you want to be recorded and displayed by the ping command. The maximum value for the count is 9. It works only with IPv4 addresses.
- /s count - reports the time (in Internet Timestamp format) when each Echo request is received and each reply is sent. The maximum value for the count is 4, meaning that only the first four hops can be time-stamped. This option works just with IPv4 addresses.
- /j host-list - uses the Loose Source Route specified in the host list. With this type of routing, successive intermediate destinations can be separated by one or multiple routers. The maximum number of addresses or names in the host list is 9. The host list is a series of IP addresses separated by spaces, and they have to be IPv4 addresses.
- /k host-list - uses the Strict Source Route specified in the host list. With strict routing, the next intermediate destination must be reachable directly (and not separated by a router). The maximum number of addresses or names in the host list is 9. The host list is a series of IPv4 addresses separated by spaces.
- /w timeout - the timeout value adjusts the amount of time, in milliseconds, that the ping waits for each reply. The default timeout value is 4000 or 4 seconds.
- /r range - tells the ping command to trace the round trip path for a number of hops. It works only with IPv6 addresses. The range must be a number between 1 and 9.
- /s srcaddr - specifies the source address to use when working with IPv6 addresses. The address must be entered after srcaddr.
- /c compartments - specifies the routing compartment identifier.
- /p - pings a Hyper-V Network Virtualization provider address.
- /4 - forces the use of the IPv4 address and it is used in conjunction with hostnames, not IP addresses. For example, write “ping /4 www.microsoft.com” (without the quotation marks), and it returns the IPv4 address of the hostname.
- /6 - forces the use of the IPv6 address and it is used in conjunction with hostnames, not IP addresses. For example, execute the “ping /6 www.microsoft.com” command to see the IPv6 address of the hostname.
Examples of ping commands
To make sure that you understand how to work with the ping command, I’ll share a few examples and explain how they are used in real life. If you want to monitor a certain website and its availability, you could use:
The command endlessly pings it and shares the time it takes to reply to each Echo request.
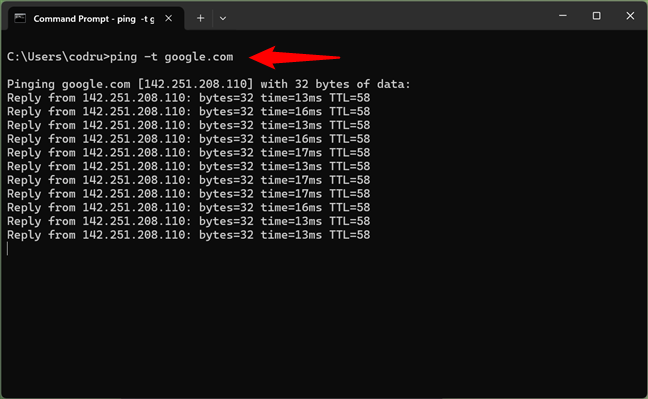
Continue sending ping commands until manually stopping
However, if you do this kind of endless monitoring of well-managed hosts, your PC could get banned from accessing. Do not forget to stop it by using your keyboard to press:
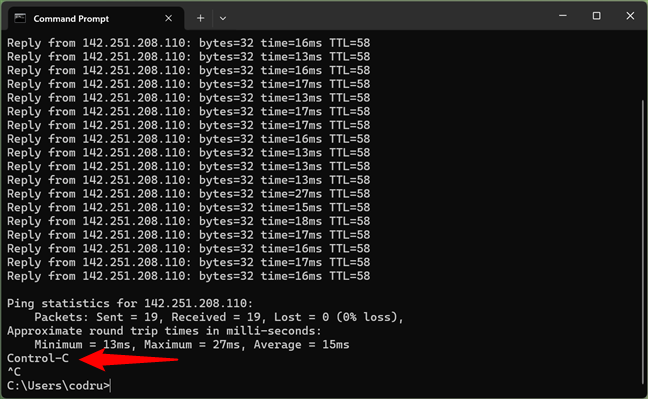
Stopping a ping command
You may want to use a finite number of Echo request messages to send, using:
…like in the next screenshot:
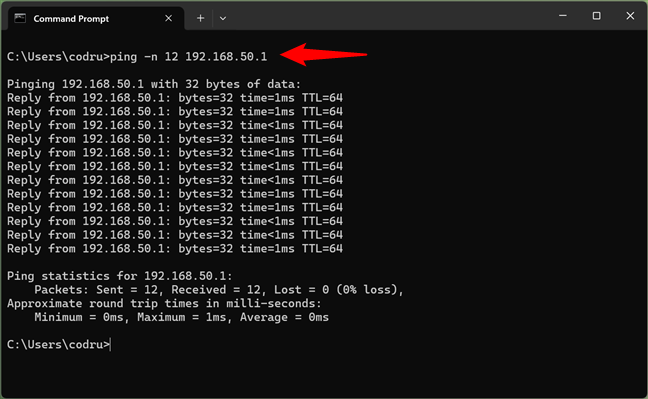
Run a specified number of ping commands
If you know the IP address of a host and you want to know the hostname, you can use:
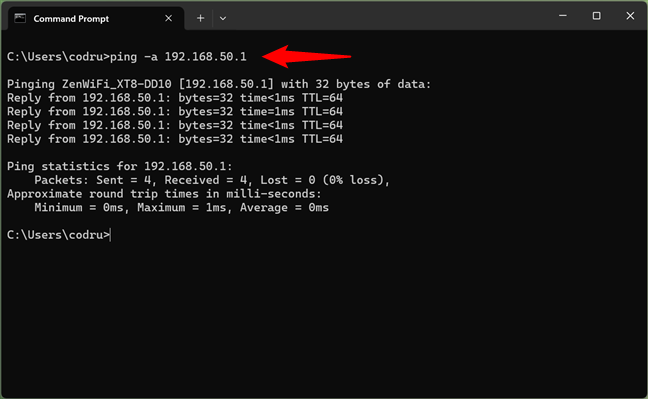
How to ping and find the name of a host
The ping tries to resolve and display the target's hostname and then returns it, similar to the previous screenshot.
Addendum: Do you know who invented ping?
The ping utility was created by an American named Mike Muuss in December 1983 while working in the Ballistic Research Laboratory at the Aberdeen Proving Ground in Maryland. The name comes from the sonar technology used in submarines, surface ships, and aircraft, which sends a pulse and listens for the echo to detect underwater objects. He found it a suitable metaphor for how the ping utility works. I like this metaphor a lot. What about you?
Do you find the ping command useful?
At the end of this article, I hope you’ve gained a better understanding of the ping command - what its purpose is, how it works, and how you can use it on your Windows computer. Have you used ping? Did it help you troubleshoot issues on your local network, on the internet, or in your favorite online game? Let me know in the comments section below.


 07.06.2024
07.06.2024