Readers of major websites like Vice News, CNET, The Verge, Neowin and more, have been exposed to security risks since 2015 because the ads they run from the PowerLinks advertising platform use expired SSL certificates. Here's what is going on, what you are exposing yourself to when reading publications that include PowerLinks ads and what you can do to stay safe:
The ads served through PowerLinks have SSL certificates that expired in October 2015
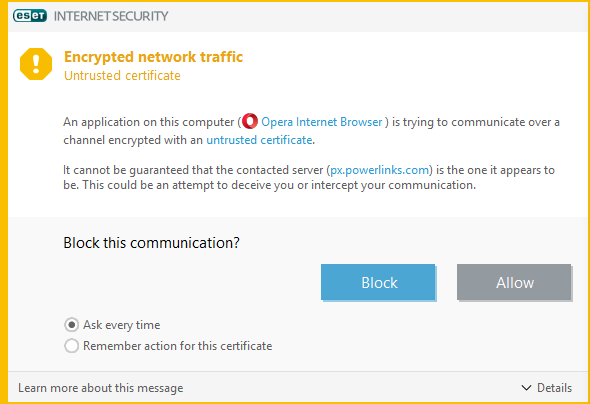
While reading several websites on my personal computer, I have noticed that my security solution was complaining that my browser is trying to communicate over a channel that is encrypted with an untrusted certificate. My antivirus could not guarantee the authenticity of the domain to which the encrypted connection was established, and this posed a security risk for me. Initially, I ignored this warning and just kept reading. However, after seeing it on several big websites, I started paying attention and studied things in more detail.
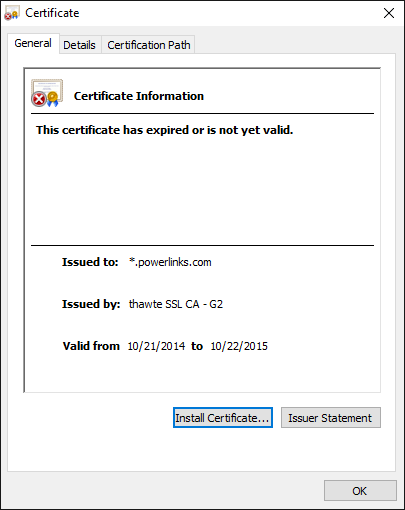
I was surprised to find that this warning is shown on large online publications and it is always caused by ads served from pw.powerlinks.com. All of them have an SSL certificate that expired in October 2015, as you can see below.
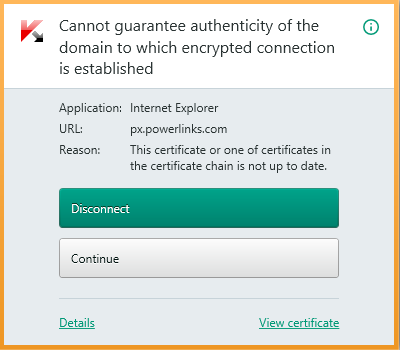
To double check whether this was true and not just a false alarm, I tried another top-notch security product, and the results were the same. I navigated more websites and noticed that the same problem was repeating for some big names in the publishing world.
What does PowerLinks offer publishers?
According to their official website, PowerLinks has a comprehensive portfolio of advertising solutions and services. They offer an Ad Server for the sites in their portfolio of clients, an Ad Exchange platform, native ads (in-text, in-video, in-image, in-feed and in-display ads) and more.
Why is this an issue? The problems we're exposed to when websites display ads with expired SSL certificates
If you don't have a good security solution installed, you might never notice this issue. However, if you use a good antivirus which scans your HTTP traffic in real-time, then you will be annoyed by a security prompt on several large media publications that use advertising services provided by PowerLinks.
Leaving the annoyance factor aside, we asked Catalin Patrascu (head of the Information Security and Monitoring Department at the Romanian National Computer Security Incident Response Team) about the security risks involved with these ads, and he stated the following:
"Theoretically, the verification of SSL certificates can be done even though they are expired. For the users that get used to this error and don't check the SSL certificate each time they get the error, there is the risk of getting redirected to malicious pages and becoming the target of man-in-the-middle attacks".
Another important thing to consider is that these ads also track user data and user behavior. This data is sent through an insecure channel, leaving it vulnerable to interception by unwanted parties.
The websites that are affected by this issue include: The Verge, Vice News, CNET, and more
We don't know the exact list of websites that are impacted by this issue. We assume that all PowerLinks customers are at risk. So far, we have identified this problem on large media publications like The Verge, Vice News, CNET, Neowin and others. These websites have dozens of millions of readers each month, and the security of their audience has been put at risk every day they have run PowerLinks ads, since October 2015.
This problem is caused by plain negligence on PowerLink's part
What we are dealing here is plain negligence. These SSL certificates have not been expired for a couple of days or a month. They have been expired since 2015 and PowerLinks are not doing their job of offering secure advertising solutions to both online publications and readers of those publications. Their technical team did not notice that their advertising platform uses SSL certificates that have been expired for years and did nothing to solve this problem while putting millions of readers at risk. Did malware creators exploit this issue? That's a good question, and we're not sure whether PowerLinks can answer. In the end, they did not even take care of basics like expiration dates.
Which security products helped me discover this issue?
The first time I found this problem was when I was navigating some of the websites I mentioned earlier and used ESET Smart Security as my antivirus.
This issue was also confirmed by Kaspersky Total Security, as you can see below.
We're pleased that these products did their job in informing us and keeping us safe from the security vulnerabilities of the PowerLinks ads platform and helps us unravel what is going on. It's further proof that you should always install a third-party antivirus product and stop browsing the web, unsecured. If you are curious to learn more about the risks involved with browsing the web unprotected, read this experiment that we have run: How to infect your Windows PC while browsing the web for free stuff.
What did we do to help readers and publications that are affected by this security issue?
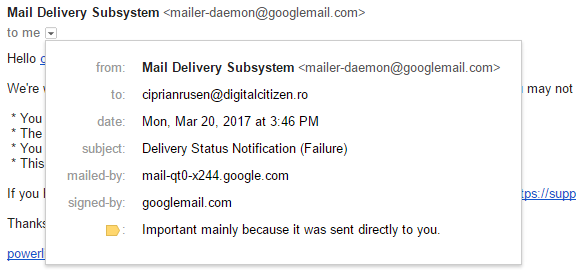
First of all, we wrote this article to inform everyone on this matter. We also asked PowerLinks for an official comment. However, their official contact e-mail doesn't work, and all we received is a Delivery Status Notification Failure, which you can see below.
We sent this article to all the media publications that we've found that are affected, as well as to PowerLinks, using their social media channels. We hope that they won't ignore our message and will take measures to fix this problem.
UPDATE (03/21/2017): We finally managed to get our message sent to PowerLinks, and we received the following answer from Branden Smythe, VP Business Development:
"I received notice that you reached out to PowerLinks. We will address the concerns you posted shortly."
Today, we checked again the websites where we have found the issues that we described and things are now working well. It seems that PowerLinks has performed the necessary steps to secure their ad delivery on all websites, which is great. Hopefully, they will learn from this problem and take better care of security basics like the expiration date of SSL certificates.
What can you do to protect yourself from insecure PowerLinks ads?
If your security solution is complaining about the expired SSL certificates used by PowerLinks ads, you should block them. If you don't have an antivirus which scans your real-time HTTP traffic, then you should run these websites using private browsing modes that also block the insecure ads or find some other way of blocking them. We are not fans of blocking ads on the websites that we have mentioned because advertising is what keeps these publications able to provide everyone with great content. Hopefully, this problem will be solved soon, and we can all enjoy our favorite publications, safely, without blocking their advertising and allowing them to earn revenue from their work.


 20.03.2017
20.03.2017