Windows stores the passwords that you use to log in, access network shares, or shared devices. Some of these passwords are stored safely, in an encrypted format, while others are not. Here is how to see which passwords are insecurely stored by Windows, and identify those that can be easily stolen by others:
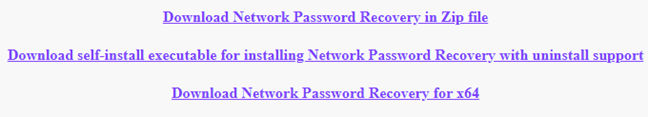
Step 1. Download Network Password Recovery, for free
First, you need an app that knows where Windows stores passwords and reads them for you. One of the best apps for this task is Network Password Recovery. It is available for free, without bloatware of any kind, both in portable and installable forms. Another positive is the fact that it is available in dozens of languages, not just English.
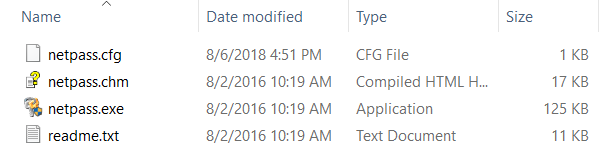
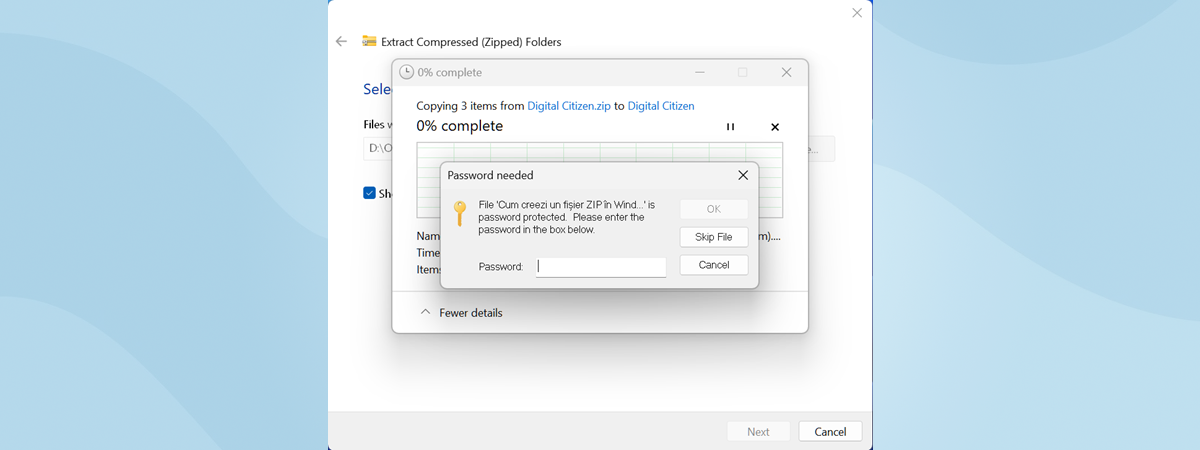
Download the netpass.zip file archive and extract it somewhere on your computer. The app can be used to read passwords from the current operating system or from an external drive where you installed Windows. The external drive can be also from another Windows computer.
Step 2. Run Network Password Recovery and see which Windows passwords are vulnerable
Next, run the netpass.exe file, and when you see a UAC prompt asking for administrative permissions to run the app, click or tap Yes.
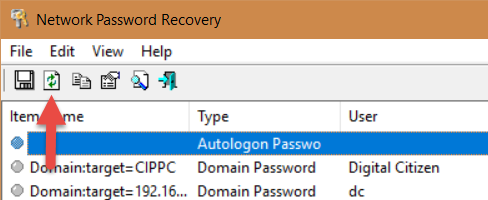
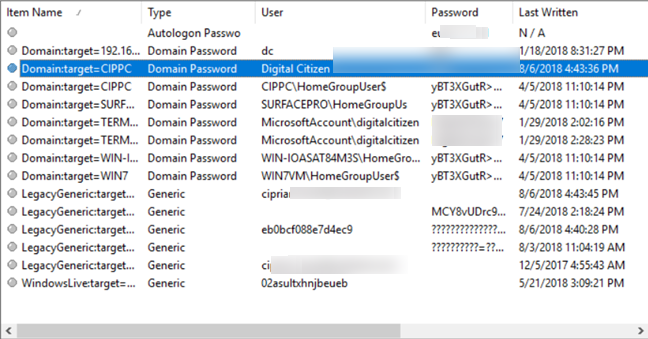
The Network Password Recovery app is loaded. It immediately displays all the passwords stored by Windows. If you want to refresh the data displayed, press the F5 key on your keyboard, or the Refresh button in its toolbar.
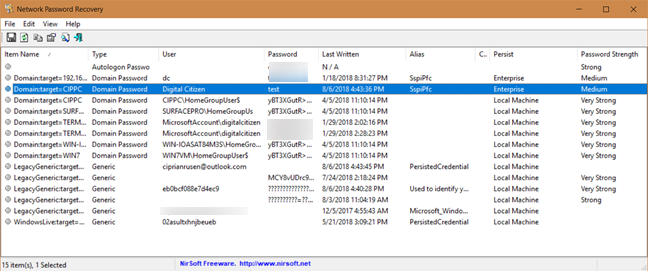
For each item in the list you see: its name stored by Windows, the type of password (generic, domain password, autologon password), the username, the password, when the password was "last written" or stored by Windows, the internal alias Windows uses, comments stored by Windows or the apps using the password, the persist value, and the password strength.
We were surprised to see that Windows store some passwords in plain text. For example, if you log into a network share using a local user account, the password gets stored in plain text, easy to read.
If you set Windows to log you in automatically, without having to type your password, then your password has become insecure. It does not matter whether you use a Microsoft account or a local user account, it is stored in plain text, easy to read by anyone. Generally, Microsoft accounts have their password stored in an encrypted format. Unfortunately, the automatic logon makes them vulnerable, and easy to read with the right tools.
With Network Password Recovery you can also read passwords used by Microsoft Outlook to connect to Exchange mail servers, or the passwords stored when using Remote Desktop. This tool reveals and shows all the data that is easy to steal by anyone with access to your Windows computer or its hard disk.
What to do when you want Windows to forget a password stored insecurely?
If your Windows password has become vulnerable because you turned on the automatic login, then you should turn off this feature. If you want Windows to forget some passwords that you use inside a network, to access shared folders and devices, then open the Credential Manager and remove them from there. This tutorial helps with all the steps you need to go through: Credential Manager is where Windows stores passwords and login details. Here's how to use it!
Which easy to read passwords did you find?
Network Password Recovery is a powerful tool that can also be used from the Command Prompt. Try it out and see what passwords are vulnerable on your PCs with Windows. Also, do not forget to take corrective measures. You never know when one of your passwords gets stolen by someone who should not have access to it.


 09.08.2018
09.08.2018