For any company, security is crucial. Employees and the way they communicate represent one of the most significant security holes. Email messages, files sent through the network, on USB memory sticks or portable hard drives, these are all things that can be intercepted relatively easily. That is why one of the most critical aspects for the security of a company or institution is how the data is encrypted and how the access to information is controlled. We would like to take a look at one of the best encryption solutions, that can be used locally but also managed remotely. It is called ESET EndPoint Encryption, and it is built from two software solutions designed for encrypting data: DESlock+, a client app that can encrypt data on workstations, and DESlock+ Enterprise Server, the administration solution for your company. Here are a few of the most useful things you can do with ESET EndPoint Encryption (DesLock+):
1. Encrypting the email messages sent by employees
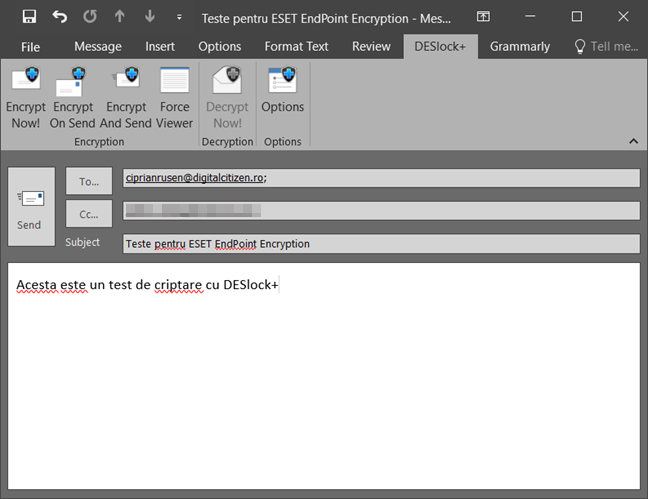
ESET Endpoint Encryption (DESlock+) offers its users the option to send encrypted email messages, with the help of a plugin that installs automatically in Microsoft Outlook, version 2003 or newer. When you want to send an encrypted message, with Outlook, you can choose one of the encryption options available in DESlock+.
When you want to encrypt an email message, you have three options: Encrypt Now!, Encrypt On Send and Encrypt And Send. The Encrypt Now! Button encrypts the email message immediately, Encrypt On Send automatically encrypts the message when you send it, and Encrypt And Send both encrypts and sends the message.
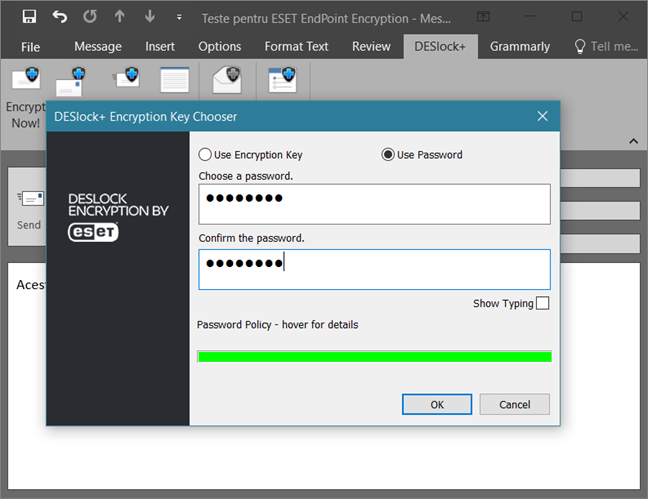
After you have pressed one of the encryption buttons, DESlock+ asks you to choose the encryption key that you want to use, or it lets you enter a password that is used as an encryption key.
When the receiver gets the encrypted email message, he or she can use DESlock+ to decrypt it. Even if he/she does not have this encryption tool installed, he/she can use the free app called DESlock+ Reader to decrypt the message, as long as the password is right.
2. Encrypting folders that have sensitive files inside
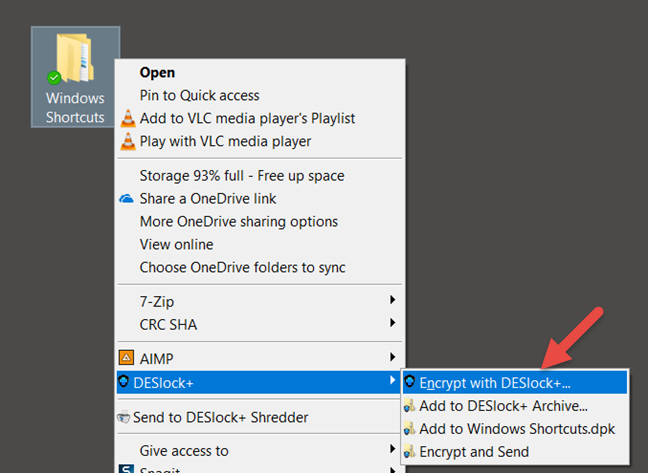
DESlock+ includes a tool for encrypting the folders that contain information to which you do not want everybody to have access. Encrypting a folder on a Windows computer is easy: right-click on that folder, go to the DESlock+ submenu and press Encrypt with DESlock+.
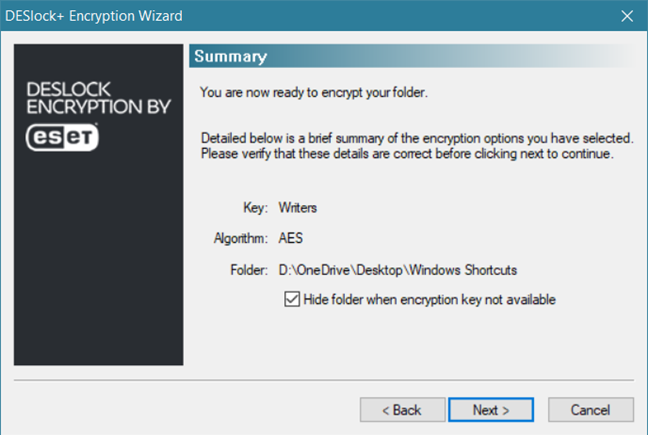
Then, DESlock+ can use one of the available encryption keys to encrypt that folder.
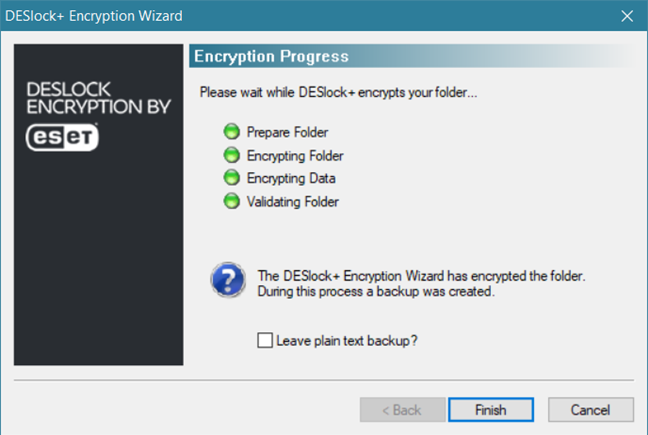
The time needed to encrypt the folder can vary a lot depending on how fast your Windows computer is and how many files are found in that folder. In the end, you can choose to keep an unencrypted copy of that folder, or you can completely remove it.
As long as DESlock+ is active on your PC, you have unrestricted access to the folders you have encrypted. However, if the DESlock+ app is stopped, those folders can no longer be accessed, as they disappear.
3. Encrypting removable drives (USB memory sticks, memory cards, portable hard drives, etc.)
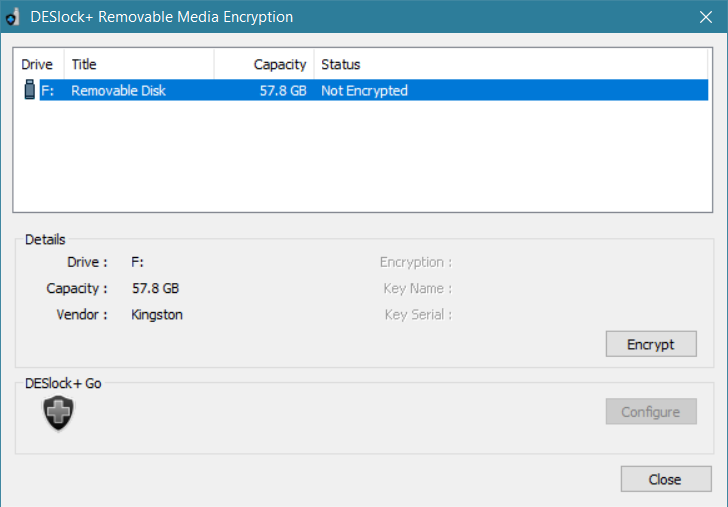
With DESlock+ you can also encrypt removable drives such as USB memory sticks, memory cards, portable hard drives or SSDs. You have to right-click on the DESlock+ icon from the system tray, choose Removable Media and then click Removable Media Encryption.
Then, DESlock+ opens a wizard in which you can choose what removable drive you want to encrypt, as well as whether you want to encrypt it entirely or partially.
Once you have started the encryption process, wait for it to finish. If you chose to completely encrypt that USB memory stick (or memory card, portable HDD, etc.), this step can take a long time.
If you chose the full encryption, that storage unit is going to be accessible only on computers that also have DESlock+ installed. If you choose to encrypt only a part of the storage unit, it can be decrypted on any PC, with the help of a tool called DESlock+ Go.
4. Encrypting text in documents
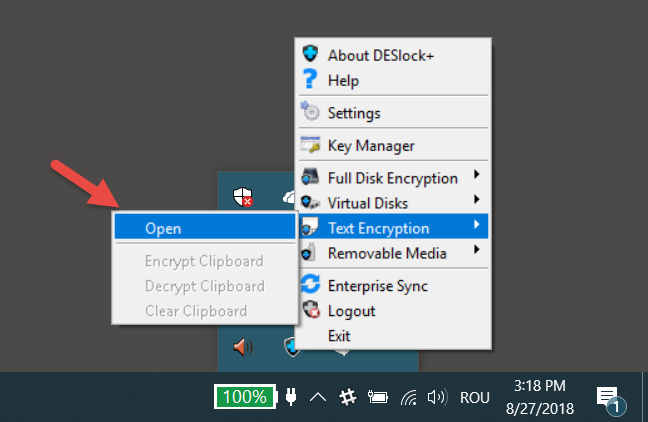
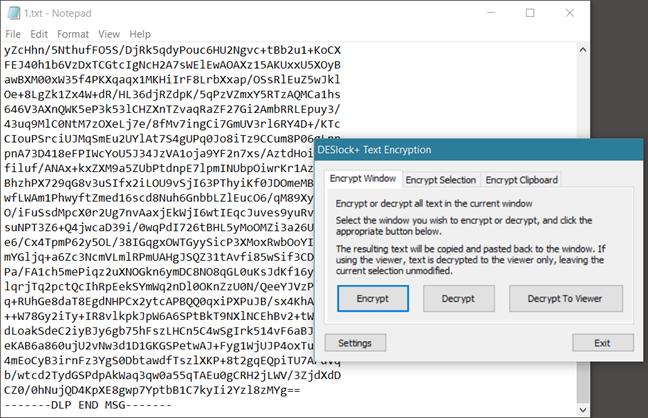
With DESlock+ you can also encrypt and decrypt text. If you want that, you have to open the DESlock+ menu from the system tray and go to Text Encryption -> Open.
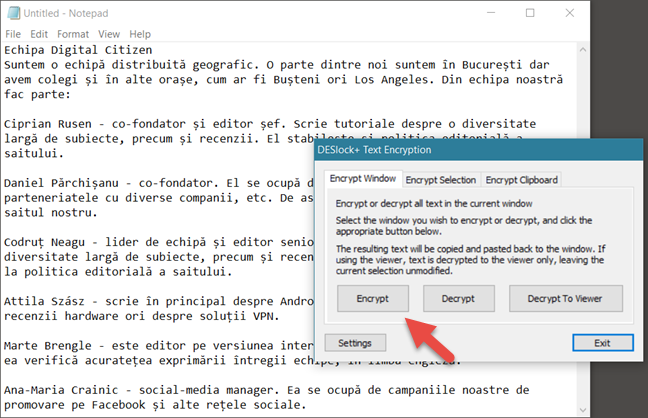
Once the DESlock+ Text Encryption opens, select the window that contains the text which you want to encrypt, or select just a part of it, if you do not want to encrypt it entirely. Then, click the Encrypt button.
You must also choose the encryption key (or the encryption password if you prefer), after which the whole selected text (or all the text in the window) is encrypted and looks like this:
To be able to decrypt that text, you need to supply the right encryption key or the right password.
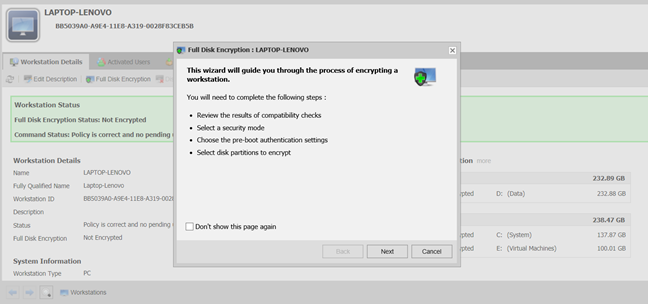
5. Encrypting whole partitions or storage units (hard drives, SSDs, etc.)
DESlock+ can encrypt entire hard drives, solid state drives or partitions. With DESlock+ Enterprise Server, you can manage all the workstations used by the employees, and you can completely encrypt them. This tool assures you that nothing on those workstations can be accessed by unauthorized personnel. The only users that can turn on and use the workstations are those authorized to do so and have the authentication details.
This type of encryption requires the authentication on the workstation before the operating system boots, which means that DESlock+ protects not only the user's files but also the operating system files, the swap files, temporary files and any files that the user once deleted but could be recovered using the right tools.
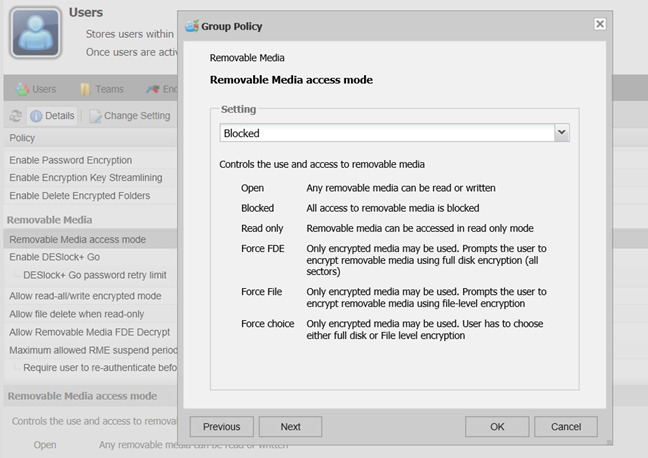
6. Configuring policies
DESlock+ Enterprise Server also comes with a policy administration system. One of the most necessary policies in any company is that which controls the access to removable drives, such as USB memory sticks. DESlock+ gives us the option to manage which users are allowed to access portable drives, completely, never or just partially, like only when they are encrypted, for instance.
In the DESlock+ Enterprise Server web interface, administrators can create such policies with ease, using the options available in the Users and Workstations sections.
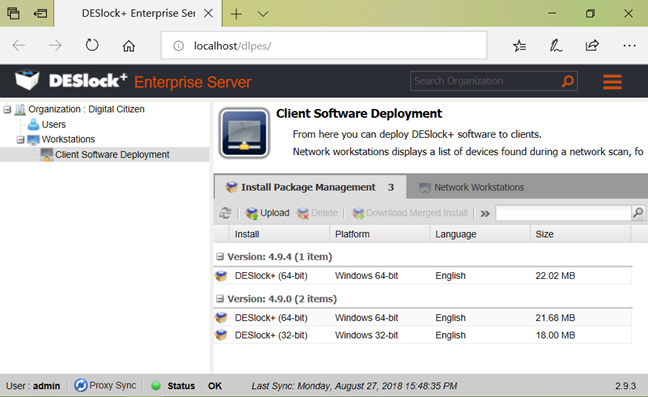
7. Remote installation of DESlock+ on workstations
DESlock+ Enterprise Server can be used by administrators to remotely install managed versions of the DESlock+ client on the workstations that they manage. To be able to do this, the client computer on which DESlock+ is going to be installed must be a part of the same network as the computer on which DESlock+ Enterprise Server is installed.
If you cannot install the DESlock+ client remotely on the workstations, there is also the option to generate an MSI file using DESlock+ Enterprise Server, which you can then manually install on the workstations.
8. Data protection that is compliant with GDPR
Europe has enforced its General Data Protection Regulation (GDPR) with strict rules for protecting personal data. GDPR also details the prevention measures that can be taken for data leaks, considered to be suitable for implementation in businesses and institutions. One of the recommendations involves data encryption.
The encryption with DESlock allows companies to meet their GDPR obligations for securing their data and applying encryption policies while maintaining high productivity. DESlock Encryption by ESET also solves one of the biggest challenges regarding applicability: how can users share all the encrypted data that they need to work with, as easily as possible? Easy-to-guess passwords are a potential security risk, while encryption with public encryption keys may cause problems, especially in large teams, with a high degree of personnel turnover. Using encryption keys that are managed centrally avoids these issues, reflecting a more natural solution, similar to the physical keys that we use to block access to a car or a house. You can learn more about the applicability of ESET EndPoint Encryption (DesLock+) concerning GDPR compliance, here.
What do you think of ESET EndPoint Encryption (DesLock+)?
Now you know the things you can do with ESET EndPoint Encryption (DesLock+). We believe that this platform could significantly improve security at the company you work at. Before closing this article, we would like to know your opinion about the features that it has to offer, in the comments section below.



 07.09.2018
07.09.2018