Everybody knows that installing lots of drivers and software on a computer increases its vulnerability from a security standpoint. As you install stuff, the complexity increases as well as the likelihood of encountering security issues. I always wanted a tool to evaluate how the security of a system evolves while installing software that you plan to use and so far I haven't found one. Luckily, Microsoft released a free evaluation tool named Attack Surface Analyzer. If you want to learn more about it and how to use it, read this article.
Must Have Prerequisite - NET Framework 4
Download and install Microsoft.NET Framework 4 (Web Installer) prior to running the setup for Microsoft Attack Surface Analyzer. If you install it after you install Attack Surface Analyzer, you will have access only to the command line version of the tool. If you prefer to use a graphical user interface, install Microsoft.NET Framework 4 prior to installing Microsoft's Attack Surface Analyzer.
You can find the Attack Surface Analyzer here.
Microsoft Attack Surface Analyzer - What Does It Do?
Complete information about the tool can be found in the Attack Surface Analyzer Readme document. I strongly recommend that you to download and read this document.
To summarize the key points, Attack Surface Analyzer does the following:
- Scans your operating system to create a baseline of its security and vulnerability level;
- It is run again at any time (after you install drivers, updates, applications, etc) to capture the changes taking place in your system;
- Compares your baseline with any subsequent scan and shares a report of what has changed from a security and vulnerability perspective.
The report includes the security issues that were detected (vulnerable executables, directories with vulnerable executables, weak registry settings, vulnerable processes, threads and services, etc.) and complete information about what has changed inside your system (running processes, open windows, system modules, services, drivers, file registrations, Internet Explorer misconfigurations, firewall rules, etc).
How to Use Microsoft's Attack Surface Analyzer
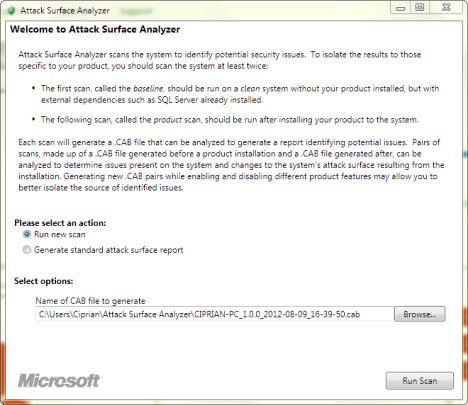
Run Attack Surface Analyzer. Make sure "Run new scan" is selected and press Run Scan.
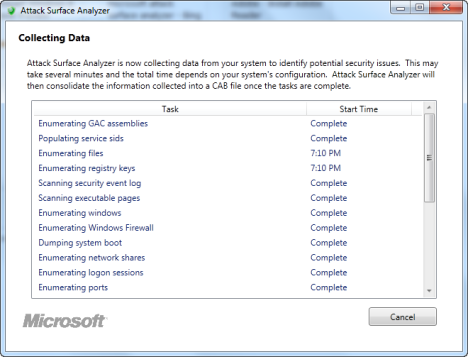
Wait for the data collection process to end. It will take a while, so arm yourself with some patience.
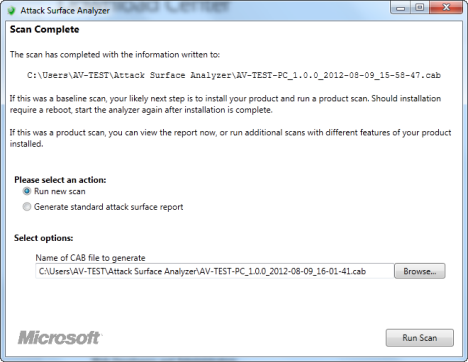
When, the data collection is done, you are returned to the initial screen and shown the path where the information from this scan was stored. This file should not be deleted as it will be the baseline against which you will make future comparisons.
After you install applications, drivers, everything you want to install and evaluate, run the tool again and make a new scan.
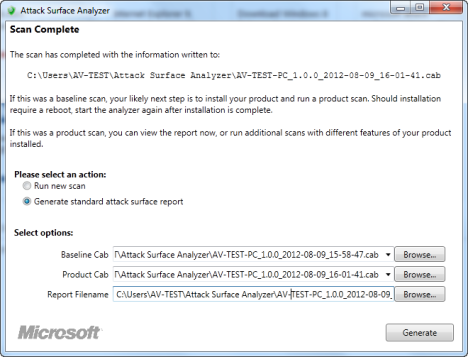
When the new scan is done, leave the tool open and select "Generate standard attack surface report".
Then, select the baseline file plus the file generated by the latest scan and press Generate.
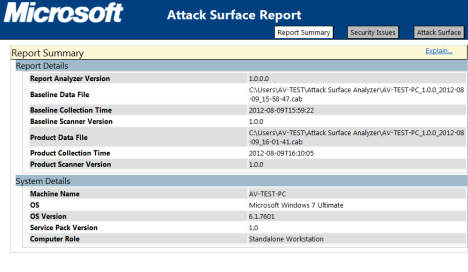
An HTML report will be shown in Internet Explorer, with three sections: Report Summary, Security Issues and Attack Surface, all displaying useful information about your system's security and how it has changed compared to the baseline scan.
When Is This Tool Useful?
The Attack Surface Analyzer is a complex tool which displays important data in a very detailed manner. Therefore, its target audience is formed mostly by professionals and power users with good technical skills.
The tool can be useful in many scenarios, including: developing new software and testing its security vulnerabilities, evaluating the security issues existing on computers that are part of a network after you install the standard software that is required, evaluating the security issues of your own computer, after installing all the software you plan to use on a regular basis.


 09.08.2012
09.08.2012