Would you like to know how many open ports are found on each computer or device that is part of your network? Do you want to evaluate how good their firewall protection is and how vulnerable they are? Then, you should try Nmap - an open source tool for security auditing. We use it in our reviews for security solutions and we think it is awesome. You should also try it out.
Introducing Nmap & Zenmap - the Security Scanner
Nmap means "Network Mapper" and it is a command line tool for network discovery and security auditing. It is free, open source and multiplatform. It can run on Windows, Linux and Mac OS X. It is capable of some really advanced stuff and that's why it is used by many network administrators and security professionals all over the world.
I mentioned that it is a command line tool. This will definitely turn off people who do not love the Command Prompt. Luckily, there is also Zenmap - a special client which provides a visual interface for Nmap.
You can download it from here: Nmap for Windows. Look for line that says "Latest release self-installer". That's the Nmap client with a visual interface for Windows. Obviously, it runs on both Windows 7 and Windows 8.
Install it on the computer from where you want to do the auditing, not on the one you want evaluated.
How to Scan the Computers & Devices on Your Network
Launch Zenmap using its shortcut on in the Start Menu (in Windows 7) or the Start screen (in Windows 8).
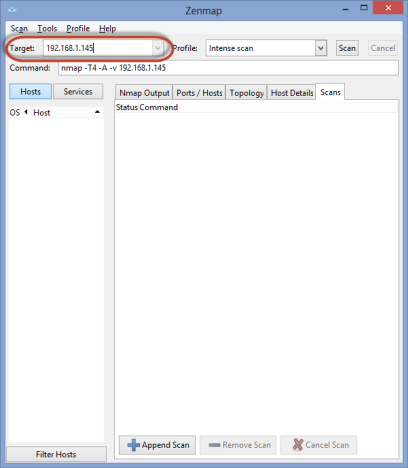
Turn on the computers and devices you want to evaluate and make sure they are connected to the network. Then, in the Zenmap window, look for the Target field. Type the IP address of the computer or devices you want to scan. You can also use the computer name, if you know it and it is more convenient.
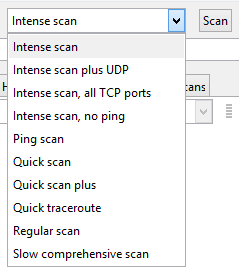
The, in the Profile field, select the type of scan you want to perform. Generally, the intense scan provides a good overview and it is over relatively fast.
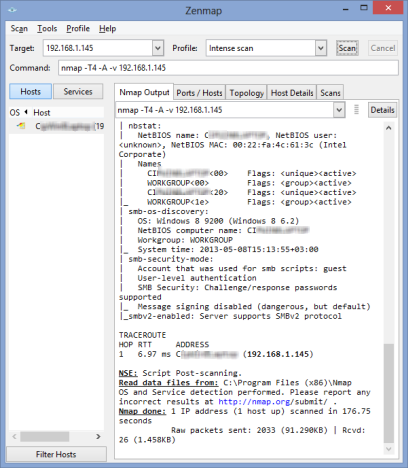
Next, press the Scan button and a UAC prompt is shown. Confirm that you want to go ahead with the scan and wait. In the Nmap Output tab, you will see lots of activity going on. When the scan is over, the last line in that tab will say "Nmap done".
Now you can read all the information displayed in the Nmap Output tab and check the other tabs available.
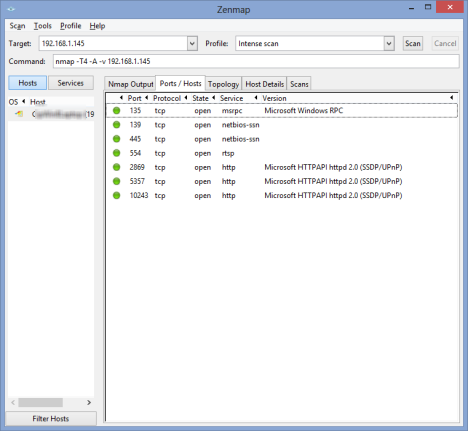
The Ports/Hosts tab lists all the ports that were found open.
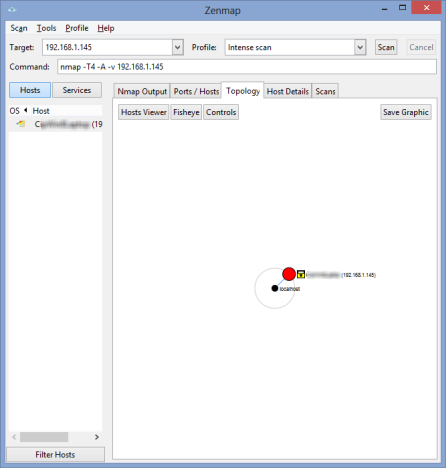
The Topology tab shares a visual overview of how the computer/device you have scanned is positioned in the network, relative to the computer from where you made the scan.
The Host Details tab shares a visual overview of the Nmap's findings. This will quickly become your favorite tab as it shares everything in a very digestible format.
The Scans tab only shares the history of the scans you have made with Zenmap.
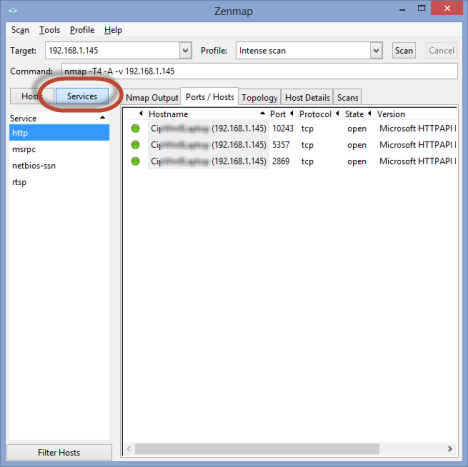
On the right, near the Hosts button, which is enabled by default, you have the Services button. Click on it, and Zenmap will filter all the information displayed in its tabs, on a per network service basis.
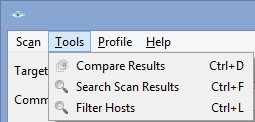
You can use the results of the scans you perform to harden the firewall protection on your network computers and devices. Then, you can perform other scans and use Zenmap to compare the results.
Zenmap stores a complete history of your scans and comparisons are easy to make, using the Tools menu.
Conclusion
As mentioned before Nmap and its visual user interface client - Zenmap, are very complex tools. In this guide I've only scratched the surface of what they can do. Therefore, don't hesitate to try them out, experiment and also read the official documentation: Nmap Reference Guide. You will find plenty of good stuff to read and learn.